

CryptPad
About this project
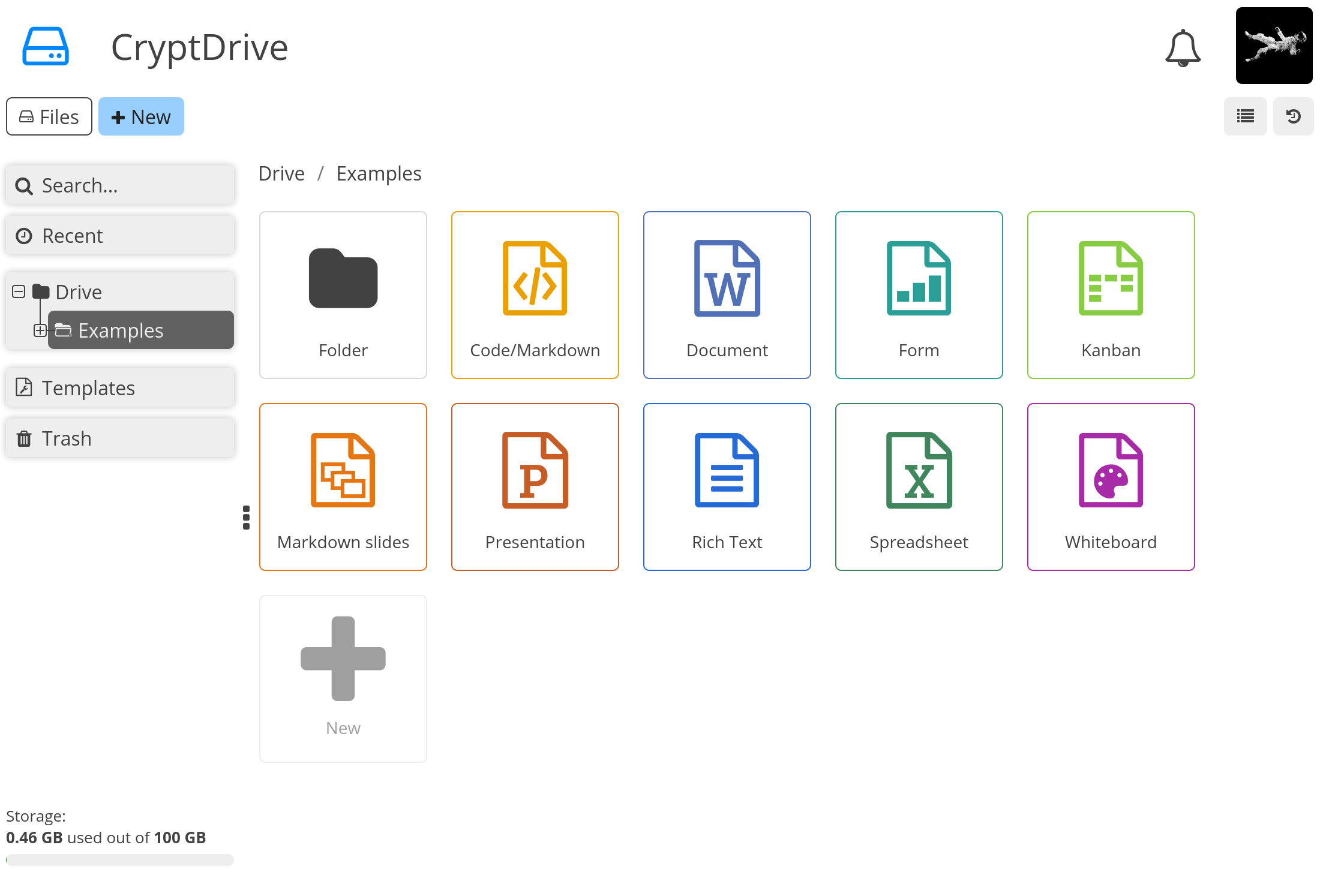
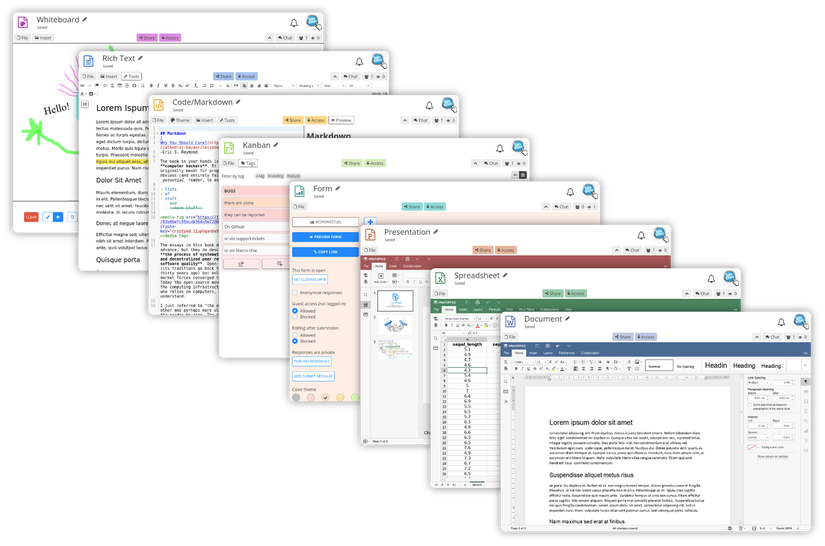
CryptPad is a collaboration suite that is end-to-end encrypted and open-source. It is designed to facilitate collaboration by synchronizing changes to documents in real time. Since all the user data is encrypted, in the event of a breach, attackers have no way of accessing the stored content. Furthermore, if the administrators do not modify the code, they and the service also cannot access any information about the users' content.
Installation
For development
Our developer guide provides instructions for setting up a local instance without HTTPS or our more advanced security features.
For production
Configuring CryptPad for production requires additional steps. Refer to our admin installation guide for production-related instructions, customization, and maintenance details.
Current version
The most recent version and all past release notes can be found on the releases page on GitHub.
Setup using Docker
You can find Dockerfile, docker-compose.yml and docker-entrypoint.sh files at the root of this repository. We also publish every release on Docker Hub as AMD64 & ARM64 official images.
Previously, Docker images were community maintained, had their own repository and weren't official supported. We changed that with v5.4.0 during July 2023. Thanks to @promasu for all the work on the community images.
Privacy / Security
CryptPad offers a variety of collaborative tools that encrypt your data in your browser before it is sent to the server and your collaborators. In the event that the server is compromized, the database holds encrypted data that is not of much value to attackers.
The code which performs the encryption is still loaded from the host server like any other web page, so you still need to trust the administrator to keep their server secure and to send you the right code. An expert can download code from the server and check that it isn't doing anything malicious like leaking your encryption keys, which is why this is considered an [active attack].
The platform is designed to minimize what data is exposed to its operators. User registration and account access are based on cryptographic keys that are derived from your username and password. Hence, the server never needs to see either, and you don't need to worry about whether they are being stored securely. It is impossible to verify whether a server's operators are logging your IP or other act
Technologies & License
Quick Deploy
Deploy this project to cloud platforms with one click