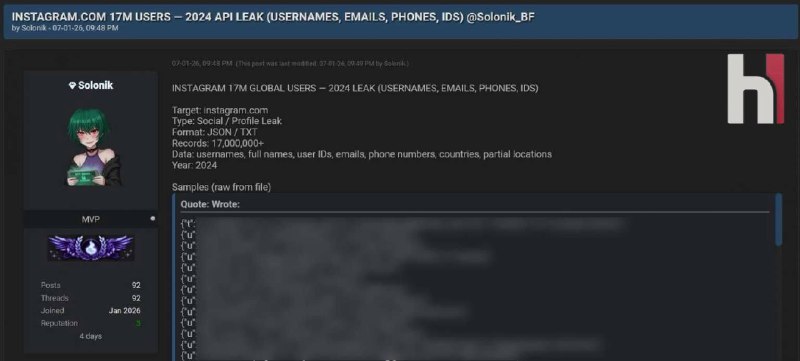
Hacktivist Exposes 500K+ Payment Records from Stalkerware Provider in Major Data Breach

A hacktivist operating under the alias "wikkid" has successfully scraped over half a million payment records from a consumer-grade stalkerware application provider, exposing sensitive customer information including email addresses and partial payment data of individuals who purchased phone surveillance services.
The compromised dataset contains transaction records from multiple surveillance platforms, including:
• Geofinder
• uMobix
• Peekviewer (formerly Glassagram) - a service claiming to provide access to private Instagram accounts
• Xnspy - a known phone surveillance application that previously suffered a data breach in 2022, exposing private data from tens of thousands of Android and iOS devices
All these services are operated by Struktura, a Ukrainian-based company. The breach represents the latest incident in a growing trend of surveillance vendors experiencing security failures that expose customer information.
Technical Details of the Breach
The exposed dataset includes approximately 536,000 records containing the following information:
• Customer email addresses
• Purchased application or brand name
• Transaction amounts
• Payment card type (Visa, Mastercard, etc.)
• Last four digits of payment cards
• Unique invoice numbers
Notably, the dataset did not include transaction timestamps. Data authenticity was verified through multiple methods, including password reset procedures on disposable email addresses with public inboxes (such as Mailinator) and cross-referencing unique invoice numbers with the vendor's checkout pages.
Exploitation Vector
According to the hacktivist, the data extraction was accomplished by exploiting a "trivial" vulnerability in the vendor's website infrastructure. The attacker stated their motivation as "having fun targeting apps that are used to spy on people." The scraped dataset was subsequently published on a known hacking forum.
Surveillance Capabilities
Applications like uMobix and Xnspy function by being installed on target devices, subsequently exfiltrating sensitive personal data including:
• Call logs and records
• SMS and text messages
• Photographs and media files
• Browser history
• Precise geolocation data
This information is then transmitted to the individual who deployed the surveillance software. These services have been explicitly marketed for spousal and domestic partner surveillance, which constitutes illegal activity in most jurisdictions.
Corporate Structure and Attribution
The hacking forum listing identified the vendor as Ersten Group, which presents itself as a UK-based software development startup. However, investigation revealed that several email addresses within the dataset reference Struktura, a Ukrainian company maintaining an identical website to Ersten Group.
The earliest record in the compromised dataset contained a $1 transaction associated with an email address belonging to Viktoriia Zosim, identified as Struktura's Chief Executive Officer.
Industry Context
This incident exemplifies a systemic security problem within the stalkerware industry. Over recent years, dozens of surveillance applications have experienced data breaches, exposing sensitive information of both customers and victims due to inadequate cybersecurity practices by operators.
Representatives from both Ersten Group and Struktura's CEO Viktoriia Zosim did not respond to requests for comment regarding the breach.
🔔 Stay tuned and subscribe →
Related news
Try these AI tools
Experience AI-driven ADHD testing with personalized insights and comprehensive reports.
SmutGPT.ai: uncensored, customizable adult AI for erotic stories with privacy and flexible plans.
Transform PDF interactions with Documind’s GPT-4 Turbo-powered chat interface. Easy upload, query, a...